OUR SOLUTIONS

WORKFORCE MANAGEMENT
Sites can consistently manage their workforce to restrict access to authorised personnel only and accurately carry out reports to know who’s on site, how far from the site they live, how long they travel and much more
View Details

DELIVERY MANAGEMENT
Site deliveries are recorded, tracked and effectively managed to eliminate complexities brought about by administrative red-tape and maximise operational efficiency by ensuring the right personnel at the right time.
View Details

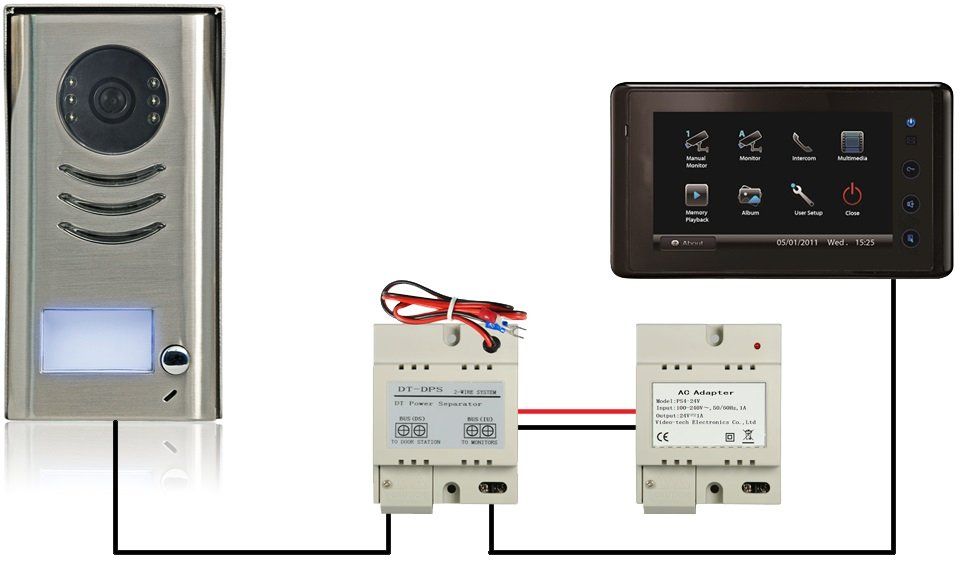
SECURITY MANAGEMENT
Physical security is provided as a priority to restrict access to the sites and tailored solutions that include access control, intrusion detection, perimeter protection and video surveillance with remote monitoring are offered.
View Details
HEALTH & SAFETY MANAGEMENT
Health and safety of staff can be managed to reduce site risks where accurate reports are produced to show the number of hours worked or to account for the workforce in the event of an incident or emergency. Our reliable fire integration system installation into your access control system which make your project, office, business, building or house more easier to function effectively in the event of fire and any emergency evacuation.
View Details

CO2 FOOTPRINT MANAGEMENT
CO2 emissions and carbon footprints can be recorded to varying degrees of detail ranging from simple average mileage calculations to more complex ones based on vehicle and engine type.
View Details

ATTENDANCE MANAGEMENT
Site managers can accurately track personnel access days or times, and generate dynamic reports making it much easier to quickly account for all authorised personnel within the site perimeter.
View Details

VISITORS MANAGEMENT
Visitors can be granted temporary access to the restricted site where visiting schedules are planned in advance where relevant passes with the required levels of access are issued for the duration of their stay.
View Details

ACCREDITATION MANAGEMENT
Sites can be enforced to ensure all authorised personnel are issued with valid employee or CSCS cards and in line with the relevant issuing bodies where access is restricted to only those with valid accreditations.
View Details
Client Testimonial

PROJECT NAME - KEYBRIDGE HOUSE
“We are pleased with their customer service, response to support requests and maintenance visits. They also have no problem relocating their equipment on site as the project progresses and requirements change. They always address our issues in a timely manner.!” – Mike Hampton














